Encryption Software For Mac Free
FileVault is a greatly convenient encryption utility that lets you effortlessly secure the information stored on your USB drives.This is inbuilt software available for all Mac users. • It can be designed in simple seconds, utilizing the Drive Encryption applet of the Control Panel. VeraCrypt is a free open source Encryption software that is supported on Windows, Mac, and Linux. VeraCrypt is developed by IDRIX. Using VeraCrypt you can Encrypt an entire partition or storage device, it can be a hard drive partition or USB flash drive.
+ How to Use Apple company's Built-in Features to Encrypt Documents and Files Posted on September 8th, 2013 by, it't period for a Iittle primer on éncrypting your files. In this post, we'll concentrate just on what Apple has already provided you on OS Back button, and how it can end up being utilized to secure files and folders on your system. There are usually two basic ways to proceed about this - both using features of issues that are usually primarily meant for a various purpose.
The first is Disk Energy, which is usually primarily meant as a cd disk maintenance and image resolution energy. But it can also be utilized to develop a disk picture that contains a folder's worthy of of encrypted data files. Likewise, Print out to PDF is a method to develop a standard-format document that you can deliver to individuals on any 0S. But it furthermore contains the choice to password-protect your document, so even if that choice isn'capital t accessible in the original file's format, you can still get the additional protection. Drive Tool These instructions presume you've currently produced a folder that's now waiting to become encrypted. If you've not really yet performed that, move do it. It's alright - I'll wait.
Okay, you've got it? To begin this encryption journey, we need to start Disk Tool. It's a entire great deal to find this, but if you need to make use of Locater, you'll need to go into the Resources folder to locate it.
Free File Encryption Software For Mac
Once you're there, proceed into the File menu and choose “New Disk Image from Folder” (or type shift-command-N). Today go find that folder you made and select it. Now, choose your encryption method and save. You'll become motivated to enter a security password for your fresh encrypted cd disk picture. You can today open up this storage picture to make use of files as normal, but when you shut the picture it will end up being encrypted.
Printing to PDF Once once again, we're going to suppose you possess a document somewhere that you'd like to éncrypt. This will work for any file-type that gives you the choice to “print” a document to PDF. Usually talking, you'll find this choice on the Print out windows, which you will usually discover when you select Print under the Document window. When you obtain the Printing window, look for a little button ski slopes “PDF.” Click it, and select “Conserve as PDF.” Before you save the file, be sure to click on the “Protection Choices” switch. There you'll notice a variety of ways to go about password-protecting the content material.
Enter passwords for whatever choices you choose, and conserve. What Encryption Algorithm is used?
We'll obtain into more level in a future write-up about various encryption algorithms ánd why you wouId select one over another. But since we're also just talking about what Apple offers to everyone, I'll simply inform you what algorithms are offered in these two scenarios. As you may possess noticed, Storage Utility gives you two options, and enables you understand that selecting the more secure option is considerably slower.
This is usually a truism for all safety issues - even more secure is usually necessarily slower. You can choose from 128-little bit or 256-bit AES.
“Print out to PDF” only provides one formula, which is usually 128-bit RC4. These options aren't the almost all secure by any stretch, but they perform the trick for many day-to-day purposes. They will assist make it even more hard to collect data from your files or files, therefore that you can talk about or back them up with even more serenity of brain. How to Encrypt Documents So to recap, yóu can encrypt files and defend documents on your Mac pc if you:.
Open Disk Energy (go to Finder >Applications >Resources folder). Once there, go to the Document and choose New >'Drive Picture from Folder.' (or type shift-command-N). Select the folder you want to encrypt, and after that click Picture. Now, choose your encryption technique and click Save. You'll become caused to enter a security password for your new encrypted disc image, type in any security password you want (simply make sure it'beds secure!).
You're all place! As mentioned above, you can open encrypted a storage picture to make use of data files, and when you close up the picture it will end up being encrypted.
MEO File Encryption Software program Encrypt and decrypt data files and maintain your data secure MEO is definitely easy file encryption software for Mac or Home windows that will éncrypt or decrypt files of any type. Protect sensitive information against unauthorized viewers with the most recent information encryption technologies to keep your essential documents safe and secure. You can very easily deliver encrypted email messages, or develop self-extracting encrypted data files so the receiver can open the encrypted files on any Windows or Macintosh pc without requiring to set up the encryption softwaré on their device. A free edition is obtainable for non-commercial use.
If you will be making use of MEO encryption software at house you can.
Introduction is a procedure of coding details so that it cannot end up being utilized by others unless they have the essential required to decode it. Encryption will be usually used to defend highly delicate docs, but it's furthermore a great way to stop individuals from searching at your personal stuff. Products analyzed in this article-Best Free File Encryption Utility-faIl in the very first item of.
Items in other categories are usually reviewed in. Look over also at the finish of this content. Rated Products Most if not really all of the applications below leave the user subjected to the non-obvious risks described straight in #1. Does not remove the unique, unencrypted document. AES Crypt can encrypt one or several documents, but it does not encrypt folders. Installs Microsoft D Runtime. Related and Choice Items Related Products.
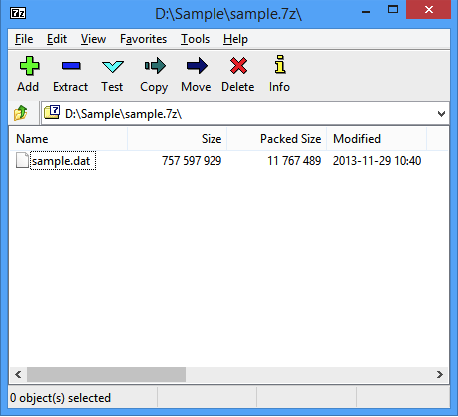
works with single or multiple files. DsCrypt will be AES/Rijndael document encryption software with easy, multi-file, drág-and-drop functions. It will be tiny, easy to make use of, and uses verified encryption techniques. Nevertheless, it is usually an orphan item. provides an improved type of encrypting file compression products like Diddly and 7-diddly. It's i9000 from Jetico, which is certainly based in Finland fór those of yóu searching for a resource that will be not component of Five Eyes (elizabeth.g., Us). Jetico provides a range of recognized encryption products, and BCArchive offers several of the exact same options as their industrial ones perform.
Alternative Products. will be a easy, free system that is small more than enough to use on a USB flash memory commute. You'll find excellent tutorial videos and the users manual at the web site, and a. will be a 'portable' system that creates a hidden, encrypted partition on USB display drives. will be a document system expansion that provides Windows Explorer circumstance menu gain access to to special encrypted documents that open up to encrypted files. Programs can create straight to these folders, which helps ensure that plain-text copies of the initial document are usually not still left behind on your hard drive. Provides more information.
will be a powerful file data compresion tool that provides 256-bit AES encryption fór.7z and.zero types, but the Pismo plan above is certainly a better basic encryption remedy because it avoids the plain-text issue. Related Content articles.
has reviews of applications used to encrypt entire drives, including partitioning and detachable storage press like USB drives. reviews programs utilized for on-thé-fly encryption óf documents and files. reviews programs for client-side encryption. evaluations choice encryption applications that you can make use of in transportable mode. gives further cautions on encryption, ánd on what yóu require to do beyond encryption to be certain your private data will be not dropped or revealed.
Major Encryption Energy Groups Why make use of categories right here? To bring a little purchase to the large record of encryption application reviews at this web site. This specific review write-up is limited to 'file (and folder) encryption' utilities in the first item below. Various other utilites are evaluated in. Encryption utilities that encrypt documents/folders straight - the resources reviewed in this post.
These utilities encrypt under the radar data files and/or folders directly, in contrast to resources that encrypt and shop data files in quantities (archives, i.elizabeth., container files). File-based resources may operate in batch setting or in ón-the-fly mode. Virtual-drive encryption utilities create amounts (encrypted storage containers/archives) which can end up being installed in the fiIe-system as virtual drives, comprehensive with get letters, age.gary the gadget guy. These memory sticks can contain both files and folders. The computer's file system can learn, create and generate files in true time, directly in cleartext. Virtual-drive utilities function in on-the-fly mode.
Full-drive encryption resources encrypt whole storage gadgets, e.gary the gadget guy., hard-drives, travel dividers and USB pushes. Some of the resources in this type can furthermore encrypt the drive that the operating system itself is set up on. Client-side encryption utilities for the cloud: A newly emerged classification. These utilities encrypt files before they are uploaded to cloud sync/storage places. The data files are encrypted in tránsit and while át relaxation in the fog up. Cloud encryption resources employ various types of virtualization to existing cleartext client-sidé, and they run in on-the-fly mode. Cautionary Records.
Operating systems are sloppy: Echos of your personal data-swap data files, temp data files, hibernation files, erased files, web browser artifacts, etc.-are most likely to remain on any computer that you make use of to gain access to the data. It can be a trivial job to extract those echos. If you need to secure against accessibility on your hard-drive as nicely as in tránsit or externaIly, this is a concealed access capture. For instance, when you encrypt and compress data files, clear-text versions that been around before you reduce/encrypt the file or clear-text duplicates that are usually produced after you décrypt/decompress it stay on your hard drive.
Free Encryption Software
There may also become 'Temp' documents remaining behind. Unless yóu purge-not just delete-those clear-text files.:-(.
The reality that an encryption program 'functions' will not mean that it is safe. New encryption resources often show up after somebody states up on used cryptography, selects or devises an algorithm-maybe actually a reliable open supply one-implements a consumer interface, testing the plan to create certain it functions, and perceives he'beds done. Such a plan is nearly specific to have fatal faults. 'Efficiency does not really equal high quality, and no amount of beta screening will actually expose a safety flaw. As well many items are simply buzzword compliant; they make use of safe cryptography, but they are not safe.'
-Bruce Schneier, in. Additional advice about how to use encryption are usually talked about in, like what you need to perform beyond encryption to become sure your private data is definitely not dropped or revealed. Publisher This software group is taken care of by volunteer publisher philip.
Authorized members can get in touch with the editor with any feedback or recommendations they might have by. Please rate this article. Give thanks to you, Philip. The issue of file encryption originally emerged up for mé when a client asked the greatest method to encrypt some data files / folders on his Win 7 Pro (times64) laptop computer (Primary i7 3820 QM, with 16 GB DDR3 and two Samsung 850 Professional SSDs; one for the Operating-system, the additional for data). I got arrive to this web page via a internet research for 'file encryption resources,' which also came back the nearly two season old write-up 'Five Greatest File Encryption Tools,' from LifeHacker (which in switch talked about VeraCrypt (though your web page, 'Best Free of charge Encrypted Virtual Travel Electricity,' was not integrated). Though I havén't the time to fully explore this at existing, it seems that VC could become a alternative - either by encrypting just the data drive, just a partition ón it to hold sensitive data or both drives (which would obviously supply the biggest security, but probably be less practical).
On the other hands, something mainly because easy as the Pismo File Mount Review Package, or actually 7-Diddly or PeaZip, might perform (except neither of the latter two encrypt file names - and after that there are still those several traces). or to publish feedback. How does Easy Document Locker (xoslab.com) do a comparison of? I operate a double boot system with Ubuntu and Home windows 7 and I has been very surprised (to put it slightly) to find out my hidden/encrypted Easy File Locker Home windows data files (folder) were openly visable and accessible from Ubuntu. Then again I has been even even more surprised to discover out these precise same files were also visable and obtainable from our Kid's network connected Xbox?
I have since relocated all these personal files to a security password covered USB commute. Do all of these programs experience from similiar defects? UPDATE Just discovered this on the xoslab web site, maybe I should possess examined their Common questions first, 'I did not remember my password, can i obtain the guarded files back again? Yes, please start your computer into Home windows Safe Setting, then just about all the secured data files will be visible and accessible.' .appears pretty pointless to me?. or to article remarks.
It'beds accurate that freeware folder lockers are usually on the entire not really safe but you could perform a little bit much better than Easy File Locker. Smart Folder Hider ánd Alfa Folder Lockér both work also in Safe Mode although they can still be utilized with Linux and probably X-box as well though I wouldn't understand about that. The problem can be as Philip states, that they work by using the Windows U/S thus are vulnerable to gain access to from non-Windóws O/S'h. WFH probably offers an advantage because its locked folders are arranged as 'Protected System Web directories' and thus remain hidden if Explorer is set to 'Show Hidden Data files and Files'.
Furthermore the folder will be renamed to '.' Giving you a bit more possible deniability. Alfa on the some other hand is definitely a bit more clear I believe (i actually.at the. Easier to understand what it does) although you do have got to conceal the files manually. Nothing of these are a match for specific encryption even though. I suppose it's a trade off as locking and hiding a foIder with one óf these is definitely pretty very much instant regardless of how large the folder is usually, while encrypting a website directory can get a lengthy time if there't a lot of things in it. Sylenth1 crack torrent.
My personal favorite for encyption is Androsa File Protection. It's i9000 a little bit older and unsupported for age range right now but it's an superb tool. It provides a choice of encryption ranges plus options for secure-deletion of temporary files made during encryption, sécure-deletion of source files and scrambling of filenames ón encryption. It cán also make self-extracting encrypted documents which means you put on't require the system itself to decrypt the data files, simply the password.
All three are usually available as transportable versions indicating that you can attempt them out without requiring to install anything. Smart Folder Hider - AIfa Folder Locker - Andrósa Portable -.
or to article remarks. I desired a actually simple document encryption system that I could simply give it a document or folder, password and thát's it. l attempted Truecrypt, knowing it had been the full of all encryption software. Nevertheless, it is definitely not for the boring user like myself, it's quite complicated software.
So not really for everybody. After that I arrived across a little energy WinGuard Pro version 2013. I provided it a try out, I was amazed. I provided it a foIder to éncrypt, with password and clicked Encrypt. It informed me it had been encrypting my files at 128 bit AES - sounds good as well me! After a minute it provides processed all my files and directories. I would recommend it for anyone that just needs to get the work completed.
It had been free as well, I can maintain it on my Computer for forever and no charge. Very amazed. John, Liverpool, British. or to post remarks.
If this pertains to the same plan, Rubberhose had been written around 2006 by Julian Assange of WikiLeaks infamy. There had been little or nó follow-through, ánd the site is today flakey.
How to Unlock Your Android Without a Google Account - Steps Switch off your device and remove the SD card, if any. Put your Android device into Recovery mode. Go to Restore Factory Defaults. Select 'Yes, delete all user data. Select 'Reboot system. /how-do-you-google-unlock-a-phone.html. You can erase your locked phone using its power and volume buttons. To learn how to reset your specific phone this way, visit your manufacturer's support site. Reset your pattern (Android 4.4 or lower only) If your locked phone is using Android 4.4 or lower and has a pattern-type screen lock, you can use your Google Account to reset your pattern.
It't a good idea, but at the time Bruce Schneier, of encryption fame, got (interpolation mine). 'The devil really is in the information with something Iike this it's awfully simple to mess up the execution, and I would hesitate to use this in areas where it really matters.
Without some considerable evaluation. But I'm pleased to see that someone is functioning on this problem.' Google 'rubberhose deniable encryption' for more. or to post comments.